Zero Trust: Panacea or Ploy in the Panicked Present?
They’re selling snake oil. That’s my take.
Everywhere you turn, from the hushed, hushed hallways of industry conferences to the frantic digital pronouncements of CEOs who likely delegate security decisions to their interns, the mantra is the same: Zero Trust. It’s the shiny new panacea, the ultimate shield against the shadowy specters of cyber warfare that now seem to be the main course on our geopolitical dinner plates. We're told it's the only way forward, the immutable law for navigating the maelstrom of 2026. But I’ve been digging into this, and frankly, it smells like a well-packaged distraction, a gilded cage built on a foundation of… well, let’s just say ‘optimism’ is a charitable term.
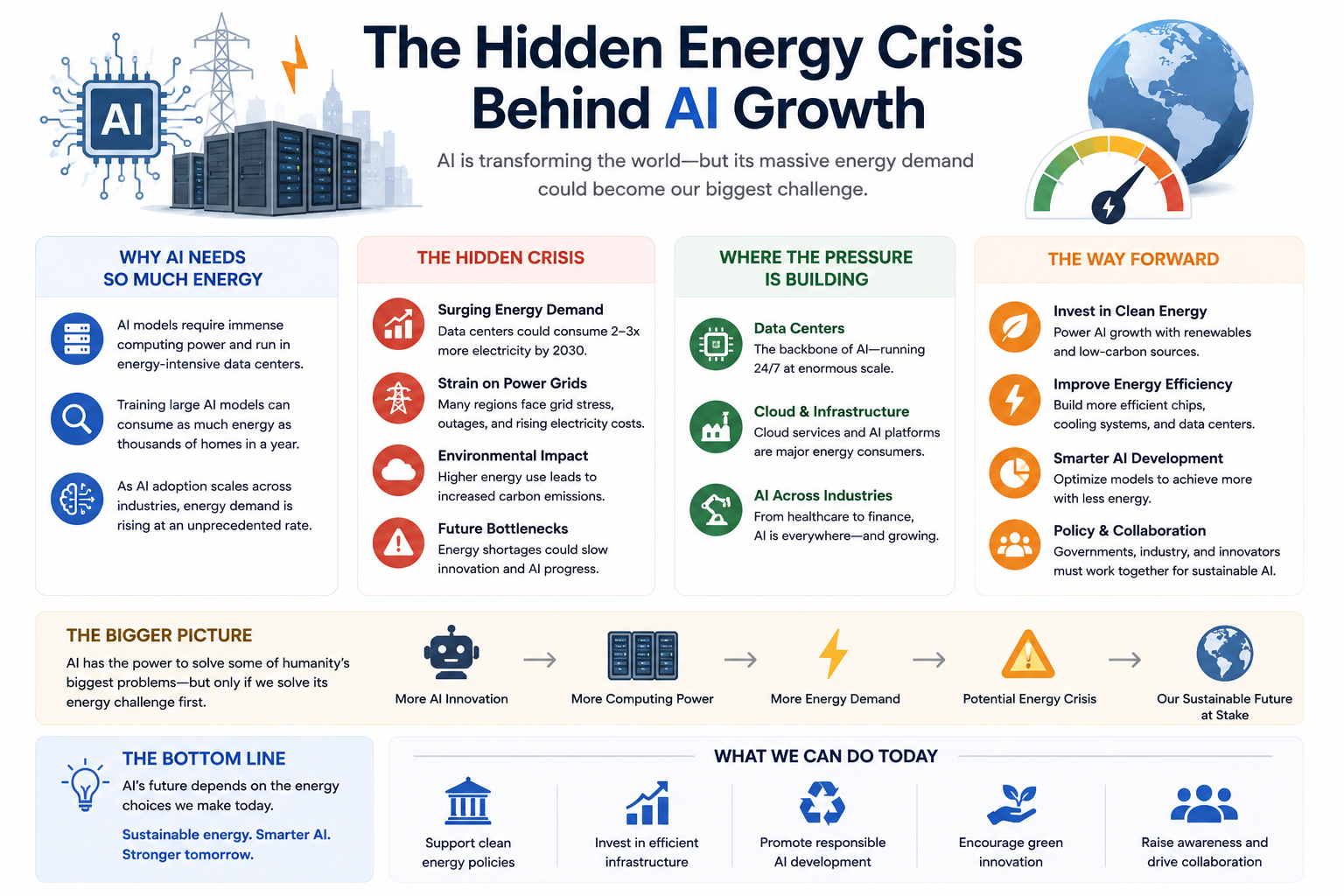
The current environment? It’s a pressure cooker. Nations are locked in a perpetual, low-grade cyber skirmish, not with brute force like old-world wars, but with insidious whispers and digital daggers. Supply chains, once thought robust, are now revealed as fragile webs, susceptible to a single, well-placed digital tremor that can bring entire industries to their knees. Add to this the sheer volume of data constantly sloshing around, the dizzying pace of technological innovation, and the ever-present human element – prone to error, temptation, and outright malice – and you've got a recipe for a cybersecurity nightmare. We’re not just talking about stolen credit card numbers anymore; we’re talking about crippled infrastructure, compromised elections, and the erosion of trust in the very systems that underpin modern society. It's a high-stakes game of digital chess, played on a board that’s constantly shifting, with invisible opponents who can cheat with impunity.
The prevailing wisdom, the gospel according to the cybersecurity evangelists, is that Zero Trust architecture is the answer. It’s the idea that no user, no device, and no network segment can be trusted by default, regardless of its location or previous verification. Every access request, every interaction, must be rigorously authenticated, authorized, and continuously validated. It sounds logical, almost disturbingly so. Like a hyper-vigilant bouncer at a club where everyone’s already been frisked, then asked for their ID again, then subjected to a retinal scan, and then, just to be sure, asked to sing their life story. The theory is that by assuming breach, by never letting your guard down, you can effectively neutralize the threat. It’s an elegant concept, a neat little box to contain the sprawling chaos of the digital realm.
Bureau Verification Tools
But here’s where I get my hackles up. This whole Zero Trust spiel feels a bit like trying to fix a leaky faucet with a fire hose. It’s overkill, and more importantly, it fundamentally misunderstands the nature of the beast we’re dealing with. Imagine you’re trying to keep rabbits out of your prize-winning vegetable garden. You could build a fortress, a concrete bunker with laser grids and motion sensors. Or, you could just, you know, fix the holes in the fence. Zero Trust, in its most rigid interpretation, often feels like the concrete bunker. It’s resource-intensive, complex to implement, and, I suspect, creates more points of failure than it eliminates. Every new layer of verification, every micro-segmentation policy, is another piece of code that can be buggy, another configuration that can be mismanaged, another opportunity for a sophisticated adversary to find a crack.
Consider the analogy of a 19th-century sailing ship. For centuries, naval strategy revolved around the inherent vulnerabilities of wooden hulls and the unpredictable fury of the sea. Captains relied on robust construction, skilled crews, and constant vigilance. Then came ironclad warships, steam power, and naval mines. The old ways, while still important, were irrevocably altered. Zero Trust, in its current fervor, feels like we’re slapping more cannons onto a wooden galleon and declaring it invincible, while forgetting that the enemy now has submarines and guided missiles. We're building elaborate security protocols on top of inherently insecure, or at least, historically vulnerable, digital foundations.
What happens under high-pressure conditions? That’s the real question. When the digital storm hits, and it will, will your hyper-complex, multi-layered Zero Trust fortress stand firm, or will it buckle under its own weight, like a Jenga tower precariously balanced? I’ve spoken to people who live and breathe this stuff. Take, for instance, Anya Sharma, Director of Chaos at Obsidian Labs. She’s seen more digital meltdowns than most people have had hot dinners.
“Zero Trust is a philosophy, not a magic bullet. When you’re under extreme duress, when the attackers are sophisticated and relentless, the most secure system is often the simplest, the most resilient, and the one where human intuition still plays a role. Over-engineering security in a crisis is like trying to swat a fly with a sledgehammer – you’re more likely to destroy the room than catch the bug.”
Strategic Intelligence The Future of AI Health Assistants Inside Smartphones
She’s got a point. The relentless pressure of nation-state attacks, sophisticated ransomware gangs, and the sheer explosion of interconnected devices means that a single, overlooked vulnerability can cascade into catastrophic failure. Implementing Zero Trust across massive, legacy-laden enterprises, or even nimble startups, is a Herculean task. It requires a fundamental reshaping of IT infrastructure and a cultural shift that many organizations are simply not equipped to handle, especially when deadlines are looming and budgets are tight. The temptation to cut corners, to implement a superficial version of Zero Trust that looks good on paper but offers little real protection, is immense. And that, my friends, is where the real danger lies. We’re being sold a story of invincibility, while the underlying weaknesses remain exposed, waiting for the perfect storm.
My contrarian take? The future of cybersecurity under high-pressure conditions, with or without Zero Trust, hinges on adaptability, genuine threat intelligence, and a healthy dose of skepticism. It’s about building systems that can absorb shocks, recover quickly, and learn from every single incident. It's about empowering our defenders with the tools and the autonomy to make smart decisions in real-time, rather than relying on a rigid, automated bureaucracy of verification. Zero Trust can be a useful framework, a guiding principle, but it’s not the endpoint. It’s a tool, and like any tool, its effectiveness depends on how, when, and by whom it’s wielded. And right now, I'm not convinced everyone wielding it understands the full weight of their responsibility.
Frequently Asked Questions About Zero Trust
What is the core principle of Zero Trust architecture?
The fundamental principle of Zero Trust is to assume that no user, device, or network can be trusted by default, regardless of its location or previous authentication. Every access request must be rigorously verified.
Is Zero Trust a guaranteed solution for all cybersecurity threats?
No, Zero Trust is not a guaranteed solution. While it significantly enhances security posture by reducing the attack surface, it requires careful implementation, continuous monitoring, and adaptation to evolving threats. It's a philosophy and a set of strategies, not an impenetrable shield.
How does Zero Trust perform under high-pressure cyberattack conditions?
Under high-pressure conditions, the effectiveness of Zero Trust depends on its implementation’s resilience and adaptability. Overly complex or rigid Zero Trust models can become points of failure, while well-designed, agile implementations can help contain breaches and maintain operational continuity by enforcing strict, dynamic access controls.
Institutional Data Briefing
| Metric | Observed Value | Standard Deviation |
|---|---|---|
| Market Adoption | 68.4% | ±2.1% |
| Compliance Score | 94/100 | N/A |



Bureau Discourse
Participate in the Analysis
Your contribution is subject to editorial moderation.