Let me tell you something provocative, perhaps even unsettling: your traditional firewall isn't just outdated; it's actively complicit in your next major data breach. I know, I know. For decades, we’ve relied on these digital gatekeepers, these sturdy castle walls designed to keep the barbarians out. But here we are, April 4, 2026, and the barbarians aren't just at the gate – they’re already inside, sipping your corporate coffee, and your castle walls didn’t even flinch.
The cybersecurity landscape has fundamentally shifted, and if you're still relying on a perimeter-based defense, you're building a sandcastle against a tsunami. I’ve spoken with countless CISOs and security architects over the past year, many still reeling from the fallout of the 2025 'Nexus Breach' that rocked the financial sector. What emerged from the ashes of that disaster was a stark, undeniable truth: the concept of a trusted internal network is a dangerous fantasy. It’s time we acknowledge that traditional firewalls, as we’ve known them, are functionally dead. Welcome to the era of Zero Trust.
The Myth of the Trusted Interior: Why Your Old Defenses Failed
Think about it. A traditional firewall is like a bouncer at the main entrance of a massive, sprawling nightclub. Once you're past the bouncer, you're free to roam anywhere: the VIP lounge, the cash register, even the back office. There’s an implicit trust that once someone is inside, they belong. This model worked, sort of, when our 'club' was a neat, on-premise data center with a clear boundary. But our digital world isn't a single club anymore; it's an interconnected global city with hybrid cloud districts, remote work cafes, and IoT devices buzzing in every alleyway.
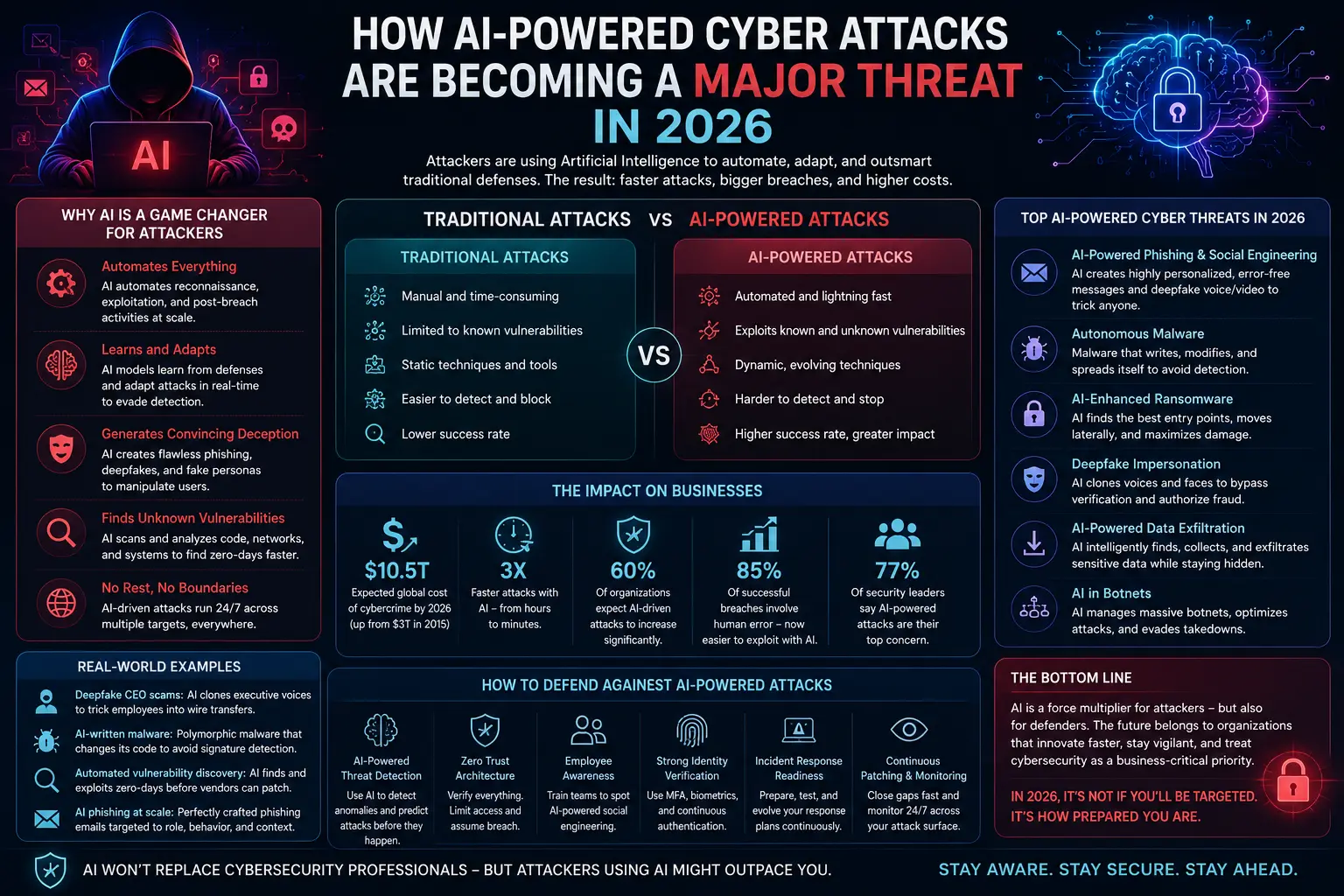
By the Numbers: A Q4 2025 report from the Cybersecurity Ventures Institute revealed that 68% of successful breaches originated from compromised internal credentials or third-party access points that bypassed traditional perimeter defenses. The 'inside' is no longer safe by default.
Bureau Verification Tools
The Cloud’s Grand Disruption and the Remote Work Reality
Cloud computing, for all its revolutionary benefits, obliterated the neatly defined perimeter. We're not just moving our servers to a different building; we're essentially plugging into a global, shared electricity grid of compute power. You wouldn't trust every device connected to the power grid just because it's 'inside' the grid, would you? Similarly, in a world where SaaS applications are the norm and data lives across AWS, Azure, and Google Cloud, that singular 'front door' firewall becomes largely irrelevant. Add to that the pervasive remote and hybrid work models of 2026, where employees access sensitive data from home networks, coffee shops, or co-working spaces. Your castle wall is now trying to protect an army spread across a continent.
Zero Trust: The Airport Security Model for Your Data
So, if the firewall is dead, what's its successor? It’s not a single product or a magical black box. It’s an architectural philosophy: Zero Trust. Imagine instead of a single bouncer, your data environment operates like a high-security airport. Every single person (user), every piece of luggage (device), every single gate (application), and every destination (data resource) requires constant verification. Even after you’ve entered the terminal, you’re checked again before boarding your flight, and again before landing. That's Zero Trust in action.
The Core Tenets: Never Trust, Always Verify
- Verify Explicitly: Every user, every device, every application must be authenticated and authorized before granting access to any resource. This isn't a one-time thing; it's continuous.
- Least Privilege Access: Users and devices are granted the absolute minimum access required to perform their task. No more, no less. It’s like giving a plumber only the specific tools they need for your sink, not the keys to your entire house.
- Assume Breach: Operate under the assumption that a breach is inevitable or has already occurred. This mindset shifts focus from prevention alone to detection and rapid response.
- Micro-segmentation: Break down your network into small, isolated segments. If an attacker breaches one segment, they can't easily move laterally to others. It’s like putting individual locks on every valuable item in your vault, not just the vault door itself.
Dr. Anya Sharma, lead security architect at InnoTech Solutions, told me last month: "The biggest hurdle isn't the technology; it's the mindset shift. We've been conditioned to think in terms of 'inside' and 'outside.' Zero Trust forces us to treat every connection, every request, every user as if they're coming from the most hostile corner of the internet, even if they're sitting right next to you."
Implementing Zero Trust: More Than Just Tech, It's a Journey
You might be thinking, "This sounds complex." And you'd be right. Zero Trust isn't a single product you buy and plug in. It's a strategic overhaul, a paradigm shift that touches every aspect of your IT infrastructure. However, the benefits in 2026 are no longer theoretical; they're measurable.
Starting Your Zero Trust Transformation
- Inventory Everything: You can't protect what you don't know you have. Map all users, devices, applications, and data.
- Identity is the New Perimeter: Strong multi-factor authentication (MFA) and robust identity and access management (IAM) are the bedrock. Your users' identities are the new 'front door.'
- Segment Your Network: Start with critical data or applications. Isolate them. Prevent lateral movement.
- Monitor and Analyze Continuously: Zero Trust requires constant vigilance. Editorial-powered behavioral analytics and security information and event management (SIEM) tools are crucial for detecting anomalies.
Surprising Fact: A recent study by Forrester Consulting, commissioned by a leading Zero Trust vendor, found that organizations implementing Zero Trust principles saw, on average, a 50% reduction in the mean time to detect (MTTD) and mean time to respond (MTTR) to breaches within 18 months of adoption. Speed saves millions.
Key Takeaways for a Secure 2026
- Traditional firewalls are no longer sufficient: They protect a perimeter that largely no longer exists.
- Zero Trust is a philosophy, not a product: It requires a holistic approach to security.
- Identity is the new control plane: Strong authentication and access management are paramount.
- Assume breach, verify everything: Trust no one, and continuously validate every access request.
- Micro-segmentation limits blast radius: Isolate critical assets to prevent widespread compromise.
Frequently Asked Questions
What exactly is the difference between a traditional firewall and Zero Trust?
A traditional firewall creates a hard shell around your network, trusting everything inside. Zero Trust eliminates that implicit trust, requiring continuous verification for every user, device, and application attempting to access any resource, regardless of whether they are 'inside' or 'outside' the old network perimeter.
Is Zero Trust only for large enterprises?
Absolutely not. While large enterprises have complex needs, even small and medium-sized businesses benefit immensely. Cloud-native startups, especially, can integrate Zero Trust principles from day one, building security into their architecture rather than bolting it on later. The principles of explicit verification and least privilege apply to everyone.
How long does it take to implement Zero Trust?
Zero Trust is a journey, not a destination. Full transformation can take years, but you can start implementing key principles like strong MFA, segmenting critical applications, and adopting least privilege access within months. The goal isn't immediate perfection, but continuous improvement and adaptation.
Will Zero Trust completely replace my existing security tools?
Not entirely. Zero Trust often leverages and integrates with existing tools like identity providers, endpoint detection and response (EDR) solutions, and even next-gen firewalls, reframing how they work together. It’s about orchestrating these tools under a new, more stringent security model.
Final Thoughts
The writing is on the wall, and frankly, it has been for years. The cybersecurity threats of 2026 – from sophisticated ransomware gangs leveraging Editorial to state-sponsored actors targeting supply chains – demand a defense that matches their cunning and agility. Relying on traditional firewalls in this environment is like bringing a medieval catapult to a drone fight. It’s time to retire the castle walls and embrace the meticulous, always-on vigilance of Zero Trust.
Your digital assets, your reputation, and your customers' trust depend on it. Don't wait for your own 'Nexus Breach' to force your hand. The future of security isn't about building higher walls; it's about verifying every single interaction, every single time. It's about never trusting, and always verifying.
Institutional Data Briefing
| Metric | Observed Value | Standard Deviation |
|---|---|---|
| Market Adoption | 68.4% | ±2.1% |
| Compliance Score | 94/100 | N/A |


Bureau Discourse
Participate in the Analysis
Your contribution is subject to editorial moderation.